1. Overview
Fyatu is committed to the security of our platform, our users, and their data. We welcome responsible security research and appreciate the efforts of the security community in helping us identify and address vulnerabilities.
This policy describes how to report security vulnerabilities to us, what is in scope, what is expected of researchers, and how we will respond.
2. Scope
The following assets are in scope for security research:
- Website — https://fyatu.com and all subdomains
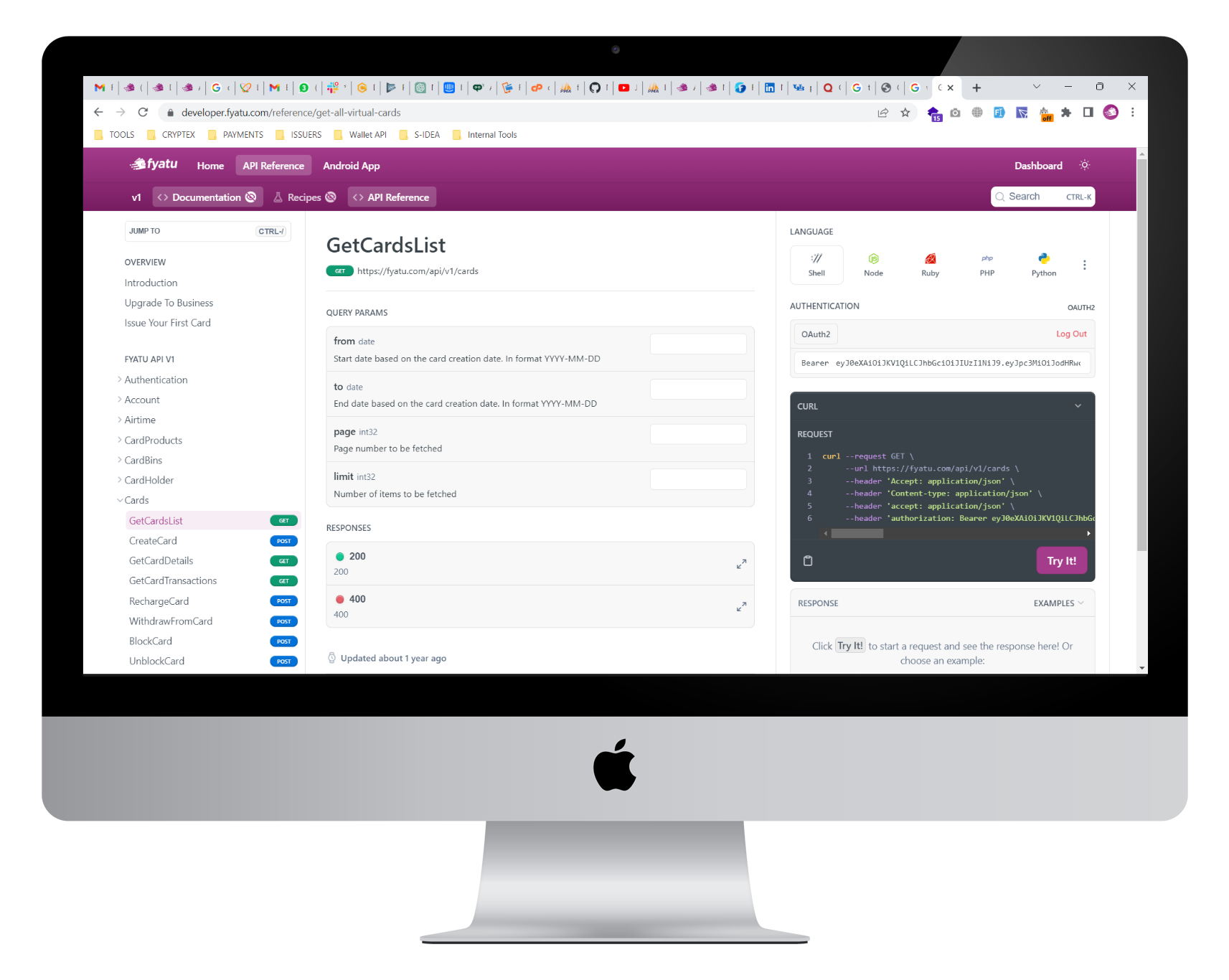
- API — All public and authenticated API endpoints
- Mobile applications — Fyatu iOS and Android apps
- Infrastructure — Any Fyatu-owned service accessible from the public internet
Out of Scope
The following are not in scope and should not be tested:
- Third-party services and integrations (payment processors, KYC providers, BIN Sponsors)
- Physical security of offices or data centers
- Social engineering attacks against Fyatu employees or users
- Denial-of-service (DoS/DDoS) attacks
- Spam or bulk messaging
- Attacks requiring physical access to a user’s device
- Vulnerabilities in third-party software that do not directly affect Fyatu
3. Qualifying Vulnerabilities
We are interested in reports covering, but not limited to:
- Remote code execution (RCE)
- SQL injection, NoSQL injection, or command injection
- Cross-site scripting (XSS) and cross-site request forgery (CSRF)
- Authentication or authorization bypass
- Insecure direct object references (IDOR)
- Server-side request forgery (SSRF)
- Sensitive data exposure or information leakage
- Privilege escalation
- Payment or transaction manipulation
- Cryptographic weaknesses in implementation
Non-Qualifying Issues
The following are generally not considered qualifying vulnerabilities:
- Missing HTTP security headers that do not lead to a demonstrable exploit
- Clickjacking on pages with no sensitive actions
- Self-XSS (where the user must inject the payload themselves)
- Rate limiting issues that do not lead to account takeover or data exposure
- Outdated software versions without a demonstrated exploit
- Brute-force attacks against login without a bypass of existing protections
- Content spoofing or text injection without demonstrated impact
4. How to Report
Send your report to [email protected]. If possible, encrypt your message using our PGP key (available upon request).
Report Form
You can also submit a report through the vulnerability disclosure form on our website.
What to Include
To help us investigate quickly, please include:
- Description of the vulnerability and its potential impact
- Affected asset (URL, API endpoint, app screen)
- Step-by-step reproduction instructions
- Proof of concept (screenshots, video, or code) if available
- Your contact information for follow-up
- Any tools or scripts used during testing
5. Our Commitment
When you report a vulnerability in good faith, we commit to:
- Acknowledge your report within 48 hours
- Assess the severity and provide an initial evaluation within 5 business days
- Remediate confirmed vulnerabilities in a timeframe appropriate to their severity
- Keep you informed of the progress toward resolution
- Credit you publicly (with your permission) on our security acknowledgments page once the vulnerability is resolved
6. Researcher Guidelines
To participate in our responsible disclosure program, you must:
- Act in good faith — Research must be conducted with the intent to improve security, not to cause harm
- Avoid data access — Do not access, modify, or delete data belonging to other users. Use your own test accounts
- Minimize impact — Do not degrade service availability or performance. Stop testing immediately if you cause unintended disruption
- Do not exploit — Once a vulnerability is confirmed, do not exploit it further or use it to access additional systems
- Maintain confidentiality — Do not publicly disclose the vulnerability until we have confirmed it is resolved and have given you written permission
- Comply with the law — Your research must comply with all applicable laws and regulations
- One report per issue — Submit a separate report for each unique vulnerability
7. Safe Harbor
Fyatu will not pursue legal action against researchers who:
- Follow the guidelines outlined in this policy
- Act in good faith and without malicious intent
- Do not access, modify, or exfiltrate user data beyond what is necessary to demonstrate the vulnerability
- Report the vulnerability directly to Fyatu and do not disclose it publicly before resolution
This safe harbor applies to legal claims under our control (such as trespass or unauthorized access) and does not bind third parties.
8. What We Do Not Offer
This is a responsible disclosure program, not a bug bounty program. We do not currently offer monetary compensation for vulnerability reports. Researchers who submit valid reports will receive public acknowledgment (with permission) and our gratitude.
9. Contact
- Security reports: [email protected]
- General support: [email protected]